Introduction
When employees work across time zones, devices, and networks, every conversation becomes a potential exposure point. According to IBM's 2024 Cost of a Data Breach Report, 40% of all data breaches involved data distributed across multiple environments — taking an average of 283 days to identify and contain.
These aren't just IT headaches. They translate into leaked strategic discussions, compromised HR data, regulatory penalties averaging $4.44 million globally, and employee trust that takes years to rebuild.
Distributed teams face compounding vulnerabilities: personal devices on unsecured networks, sensitive conversations scattered across unsanctioned apps, and insider threats that regulatory frameworks struggle to contain.
Securing internal communications in this environment requires more than the right technology. It demands a cultural commitment — one where every team member understands their role in keeping company communications safe. This guide covers the practices that make that possible.
TL;DR
- Distributed teams face heightened security risks from tool sprawl, personal devices, and multi-timezone attack surfaces
- Core safeguards: end-to-end encryption, multi-factor authentication, role-based access controls, and retention policies
- Employee behavior drives most breaches—training and channel policies are as critical as technical controls
- Top mistakes include using consumer apps for work, ignoring offboarding access, and skipping permission audits
- Unified platforms eliminate tool fragmentation by consolidating communications into governed, auditable channels
Why Distributed Teams Face Unique Communication Security Risks
Distributed teams communicate across more channels, devices, time zones, and networks than co-located teams—each touchpoint is a potential entry point for threats. Unlike office environments where IT can monitor traffic and enforce perimeter security, distributed work scatters sensitive communications across home Wi-Fi networks, coffee shop hotspots, personal smartphones, and cloud services IT may not even know exist.
External threats have evolved to exploit this fragmentation. Microsoft's 2024 Digital Defense Report documented a 146% rise in Adversary-in-the-Middle phishing attacks, many using AI-generated impersonation of executives or HR personnel to trick remote employees into surrendering credentials. CISA's Scattered Spider advisory revealed threat actors posing as IT helpdesk staff via phone calls or SMS to obtain credentials and MFA codes from employees working from home. Ransomware groups actively target communication archives, knowing that distributed teams often lack the backup and recovery infrastructure of centralized offices.
Insider Risk Is Just as Dangerous
The Verizon 2025 Data Breach Investigations Report found that internal actors accounted for 30% of breaches in the healthcare sector, with privilege misuse driving 825 incidents. IBM's research showed that malicious insider attacks resulted in the highest average breach costs at $4.92 million.
These aren't just disgruntled employees stealing data. They include well-meaning team members who use personal WhatsApp groups, consumer Slack channels, or unsanctioned file-sharing tools to "get things done" when official channels feel cumbersome.
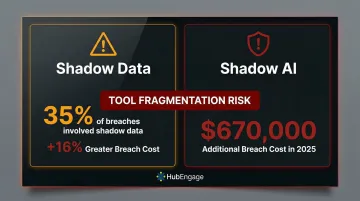
Tool fragmentation compounds this problem. When employees spread work conversations across personal messaging apps, unauthorized cloud storage, and consumer collaboration tools, sensitive information escapes the organization's security perimeter entirely. IBM's 2024 report found that 35% of breaches involved shadow data, correlating to a 16% greater cost. In 2025, organizations suffered an additional $670,000 in breach costs when incidents involved shadow AI tools employees had adopted without IT approval.
That same fragmentation creates a direct compliance exposure — one that regulators are actively penalizing.
Compliance Pressure in Distributed Environments
Regulated industries have specific legal obligations around how internal communications are stored, accessed, and audited. Distributed teams complicate every one of them by spreading conversations across unmonitored channels.
Two frameworks create the most immediate pressure for US-based organizations:
- HIPAA's Security Rule requires organizations to "implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems"
- GDPR Article 30 mandates that controllers "maintain a record of processing activities"
Recent enforcement actions show what happens when distributed communications go unmonitored:
- Solara Medical Supplies settled for $3 million after HHS OCR found the entity failed to implement proper security measures following a phishing attack on employee email accounts
- Lafourche Medical Group paid $480,000 after a phishing attack compromised an owner's email, with regulators citing failure to review information system activity
- Poland's DPA fined mBank €928,498 after an employee mistakenly sent customer documents to an unauthorized recipient

Distributed teams amplify these risks because communications that would have occurred in monitored office systems now happen across personal devices, consumer apps, and home networks that compliance frameworks never anticipated.
Core Security Practices for Internal Communications in Distributed Teams
Distributed teams create multiple entry points for data exposure—across devices, networks, time zones, and platforms. Organizations need overlapping controls that protect data at rest, in transit, and in use, without making it harder for employees to actually communicate.
End-to-End Encryption and Secure Channel Design
End-to-end encryption ensures messages and files are unreadable to anyone except the intended recipients—including the platform provider. NIST defines it as encryption applied while data passes through a network, protecting communications even if the network itself is compromised. This standard should extend across messaging, video calls, document sharing, and file transfers.
Many consumer tools and legacy intranet systems fall short here. The HIPAA Journal notes that apps like WhatsApp should not be used for protected health information because "there are no audit trails or event logs"—and they lack the ability to terminate access, monitor logins, or detect unauthorized modifications.
Organizations should evaluate encryption standards rigorously. ISO/IEC 27002:2022 Control 8.24 requires establishing rules and procedures for effective use of cryptographic techniques to protect information. For distributed teams accessing systems across untrusted networks, NIST SP 800-46 Rev. 2 advises assuming external networks cannot be trusted and mitigating risks using encryption and mutual authentication.
Authentication and Device Security
Multi-factor authentication (MFA) is the minimum requirement for accessing any internal communications platform. Microsoft research found that MFA reduces the risk of compromise by 99.22% across the entire population, and CISA states that MFA makes accounts 99% less likely to be hacked. This protection is especially critical for remote employees accessing systems from personal devices where credential theft through phishing or malware is more likely.
Strong authentication, though, only covers part of the risk. The Verizon 2025 DBIR found that 46% of compromised systems hosting corporate logins were non-managed devices—a figure tied directly to BYOD programs and devices used outside permissible policies. Organizations must decide between BYOD policies with managed security profiles versus fully company-managed devices, with clear enforcement either way.
CISA's Scattered Spider advisory recommends implementing FIDO/WebAuthn authentication or PKI-based MFA, as these are resistant to phishing, push bombing, and SIM swap attacks that increasingly target remote workers.
Role-Based Access Controls and Information Governance
Not every employee should have access to every channel, document, or conversation. Role-based access controls (RBAC) ensure that sensitive communications reach only those with a legitimate need, limiting the potential damage if an account is compromised.
In practice, this means segmenting access by function and sensitivity level:
- HR policy updates visible only to managers communicating changes to their teams
- Financial forecasts restricted to leadership channels
- Product development discussions accessible only to relevant project teams
Without these controls, a single compromised account gives an attacker—or a malicious insider—a direct path to the organization's most sensitive information.
Retention policies matter for both security and compliance. Automatic archiving and deletion schedules limit exposure of old data while meeting regulatory record-keeping requirements. The Verizon DBIR 2025 reports that privilege misuse is predominantly driven by unapproved or malicious use of legitimate privileges, with 90% of these threat actors being internal. Limiting what data exists and who can access it directly reduces this risk.

Former employee access is a persistent vulnerability. A 2022 BeyondIdentity survey found that 83% of respondents continued accessing accounts from their previous employer after leaving, with more than a third still accessing company email and work materials on personal devices. ISO 27001:2022 Annex A Control 5.18 dictates that staff leaving the organization should have access removed as soon as possible, ideally within 24 hours of departure.
Building a Security-Conscious Communication Culture Across Distance
Technology alone cannot secure distributed communications—human behavior is the most common point of failure. Distributed teams lack the informal guardrails of office environments where colleagues can see who's looking at sensitive documents or overhear suspicious phone calls. Security awareness must be built deliberately through training, clear policies, and psychological safety.
Role-specific training works better than generic annual compliance modules because it connects directly to daily work. Employees need to recognize phishing in a Teams message, understand why personal SMS isn't appropriate for sensitive updates, and know which channels are approved for which types of information.
The scenarios vary by role. Healthcare staff need to understand HIPAA implications of texting patient information. Finance teams need to spot business email compromise attempts. Remote workers need to know the risks of public Wi-Fi.
Define Which Tools Are Approved for What
Organizations should explicitly document approved channels for each communication type:
- Instant messaging platforms for quick updates and coordination
- Encrypted platforms for sensitive HR communications
- Intranet for policy documents and company resources
- Video conferencing for meetings requiring face-to-face interaction
- Email for formal communications and external correspondence
Clear policies matter because usability does too. When approved tools are easy to access, employees follow the rules. When they're not, workers find their own solutions—and shadow IT spreads.
Psychological safety rounds out the cultural foundation. Employees need to feel comfortable flagging suspicious messages or accidental data shares without fear of blame. Leaders set the tone by treating incident reports as positive behavior, not failures. In distributed environments where employees work independently without direct supervision, that kind of trust isn't optional—it's what makes everything else work.
Common Security Mistakes Distributed Teams Make
Distributed teams often make predictable security mistakes, especially during rapid growth or emergency remote transitions. Understanding these patterns helps organizations avoid them.
The five most common mistakes are:
- Using consumer apps for work — Personal WhatsApp groups, Gmail, or free Slack workspaces create unmonitored data channels that can't be audited, archived, or protected if a device is compromised
- Assuming "has a login" means "secure" — Authentication is not the same as encryption, access controls, audit trails, or retention policies
- Over-permissioning new hires from day one — Broad access configurations turn every employee into a potential insider threat, whether intentional or not
- Never auditing access as the team scales — Role changes, departing contractors, and former employees leave behind active credentials that accumulate over time
- Sending sensitive information to the wrong recipient — The Verizon 2025 DBIR found misdelivery accounted for 72% of error-based incidents involving end-users

Two of these mistakes have produced costly real-world consequences worth examining.
Consumer app usage isn't just a policy inconvenience — it's a compliance risk. In July 2024, several Aveanna Healthcare employees emailed PHI of 10,482 individuals from personal accounts, triggering regulatory scrutiny. Personal tools have no enterprise audit trail and no remote wipe capability.
Access creep compounds quietly until it doesn't. In a 2021 incident settled in 2025, a hacker accessed Illuminate Education's network through an undeactivated former employee's admin credentials, exposing personal data belonging to millions of students. A routine access review would have closed that door.
Choosing a Secure Platform for Distributed Team Communications
Consolidating communications onto a single, purpose-built platform reduces the security gaps that come from tool fragmentation. Organizations should evaluate platforms on encryption standards, access control granularity, compliance certifications, audit trail capabilities, and multi-channel delivery.
Key evaluation criteria include:
- Encryption coverage across messages, files, and video—both in transit and at rest
- Role-based permissions that let administrators restrict channels and separate sensitive information by group
- Compliance certifications relevant to your industry—SOC 2, ISO 27001, GDPR, or HIPAA
- Audit logs comprehensive enough to track who accessed what, when, and from where
- Multi-channel delivery across mobile, web, email, SMS, and digital displays so employees stay within governed channels
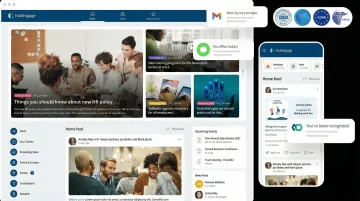
As a reference point, HubEngage meets each of these criteria for distributed and frontline teams. The platform covers mobile apps, web intranet, email, SMS, and digital displays with role-based access controls—and holds ISO 27001, SOC, GDPR, and HIPAA certifications.
Adoption matters as much as features. A platform with too much friction will push distributed workers toward workarounds that carry far greater risk. When security and usability work together, employees naturally stay within governed channels—reducing the organization's attack surface without constant enforcement.
Frequently Asked Questions
What are the biggest security risks in internal communications for distributed teams?
The primary risks include tool sprawl where employees use multiple unsanctioned apps, unsecured personal devices accessing company systems, social engineering attacks targeting remote workers, and insider threats from accidental data sharing through unauthorized channels.
How does tool fragmentation create communication security vulnerabilities?
When employees use multiple unsanctioned apps, sensitive information spreads across channels the organization cannot monitor, archive, or protect. This gaps exposes the organization to breach risk and compliance violations, while making consistent security controls nearly impossible to enforce.
What is end-to-end encryption and why does it matter for internal communications?
End-to-end encryption ensures only the intended recipients can read messages, protecting sensitive data even if the communication platform itself is compromised. For distributed teams sending messages across home networks, public Wi-Fi, and personal devices, that layer of protection is what stands between your data and an attacker.
How do you ensure secure communication with frontline or deskless employees?
Frontline workers often use personal devices and may default to consumer apps. Organizations should provide a mobile-first, easy-to-use platform with built-in security so employees have no reason to reach for WhatsApp or another unsanctioned app instead.
What access controls should every distributed team put in place?
Start with these three controls:
- Multi-factor authentication for all platform access
- Role-based permissions that limit sensitive information to those who need it
- Regular access audits to revoke credentials for former employees and contractors
How do you build a security-aware culture in a remote or distributed workforce?
Focus on role-specific training that addresses actual communication scenarios, clear channel policies that define what tools are approved for what purposes, and psychological safety that encourages employees to report security concerns without fear of blame.